Shellcode loader
Features :
- Indirect syscall.
- Module stomping.
- Load a stomped module using APC.
- Execute the payload with a direct jump (jmp) without creating a new thread.
- API hashing implemented using the DJB2 algorithm.
- Payload encrypted with RC4 and encoded in UUID format, implemented directly in the loader without loading rpcrt4.dll.
- No CRT is used.
How to use :
python3 utils.py C:\Path\To\beacon.bin
Copy the output in payload.h and build the project
NB :
- If your shellcode lacks evasion features (e.g., Cobalt Strike without UDRL), it can be detected by AV/EDR
Compiling this executable and using it directly can be risky, as it may expose potential Indicators of Compromise (IOCs), such as:
- The file was compiled within the last 5 minutes.
- The Import Address Table (IAT) is empty.
Also
- If you're using a beacon, avoid using an IP for C2 communication. Instead, use a redirector with a good reputation.
- Add an icon to the executable.
- Sign the executable; ideally, use a trusted signature.
- Add delay and sandbox detection.
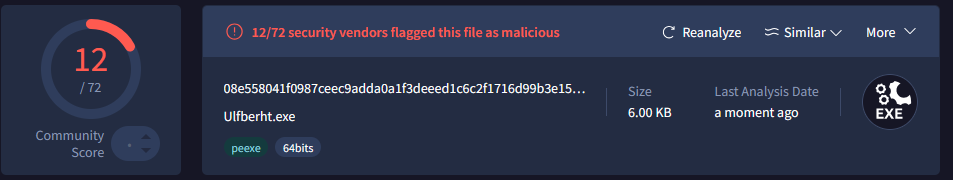
Payload after compilation
Payload after compilation with an icon
Payload after compilation with an icon and fake signature