A Python3 terminal application that contains 400 Neo4j cyphers for BloodHound data sets and a customqueries.json file containing 383 cyphers for the GUI.
BloodHound is a staple tool for every red teamer. However, there are some negative side effects based on its design. I will cover the biggest pain points I've experienced and what this tool aims to address:
- My tools think in lists - until my tools parse exported
JSONgraphs, I need graph results in a line-by-line format.txtfile - Copy/pasting graph results - this plays into the first but do we need to explain this one?
- Graphs can be too large to draw - the information contained in any graph can aid our goals as the attacker and we need to be able to view all data efficiently
- Manually running custom cyphers is time-consuming - let's automate it :)
This tool can also help blue teams to reveal detailed information about their Active Directory environments as well. Matter-of-fact, there are enough cyphers packaged within this project to allow complete visibility into an Active Directory environment. The nature of the cyphers allow the operator to enumerate the environment with scalpel precision, mapping virtually every and any attack path/privilege possible.
Take back control of your BloodHound data with cypherhound!
- 400 cyphers as of date
- Set cyphers to search based on user input (user, group, and computer-specific)
- User-defined regex cyphers
- User-defined exporting of all results
- Default export will be just end object to be used as target list with tools
- Raw export option available in
grep/cut/awk-friendly format
customqueries.jsonfile included- Run the same queries from the GUI
Make sure to have python3 installed and run:
python3 -m pip install -r requirements.txt
Start the program with: python3 cypherhound.py -c config.json
The program will read a configuration file in json format. An example of this file is shown below:
{
"user": "neo4j",
"pwd": "password",
"database": "neo4j"
}where:
useris yourNeo4jusernamepwdis yourNeo4jpassworddatabaseis yourNeo4jdatabase
The full command menu is shown below:
Command Menu
set - used to set search parameters for cyphers, double/single quotes not required for any sub-commands
sub-commands
user - the user to use in user-specific cyphers (MUST include @domain.name)
group - the group to use in group-specific cyphers (MUST include @domain.name)
computer - the computer to use in computer-specific cyphers (SHOULD include .domain.name or @domain.name)
regex - the regex to use in regex-specific cyphers
example
set user [email protected]
set group domain [email protected]
set computer dc01.domain.local
set regex .*((?i)web).*
run - used to run cyphers
parameters
cypher number - the number of the cypher to run
example
run 7
export - used to export cypher results to txt files
parameters
cypher number - the number of the cypher to run and then export
output filename - the number of the output file, extension not needed
example
export 31 results
list - used to show a list of cyphers
parameters
list type - the type of cyphers to list (general, user, group, computer, regex, all)
example
list general
list user
list group
list computer
list regex
list all
search - used to search the list of cyphers
parameters
search query - the search string
example
search domain admin
search shortest
q, quit, exit, stop - used to exit the program
clear, cls - used to clear the terminal
help, ? - used to display this help menu
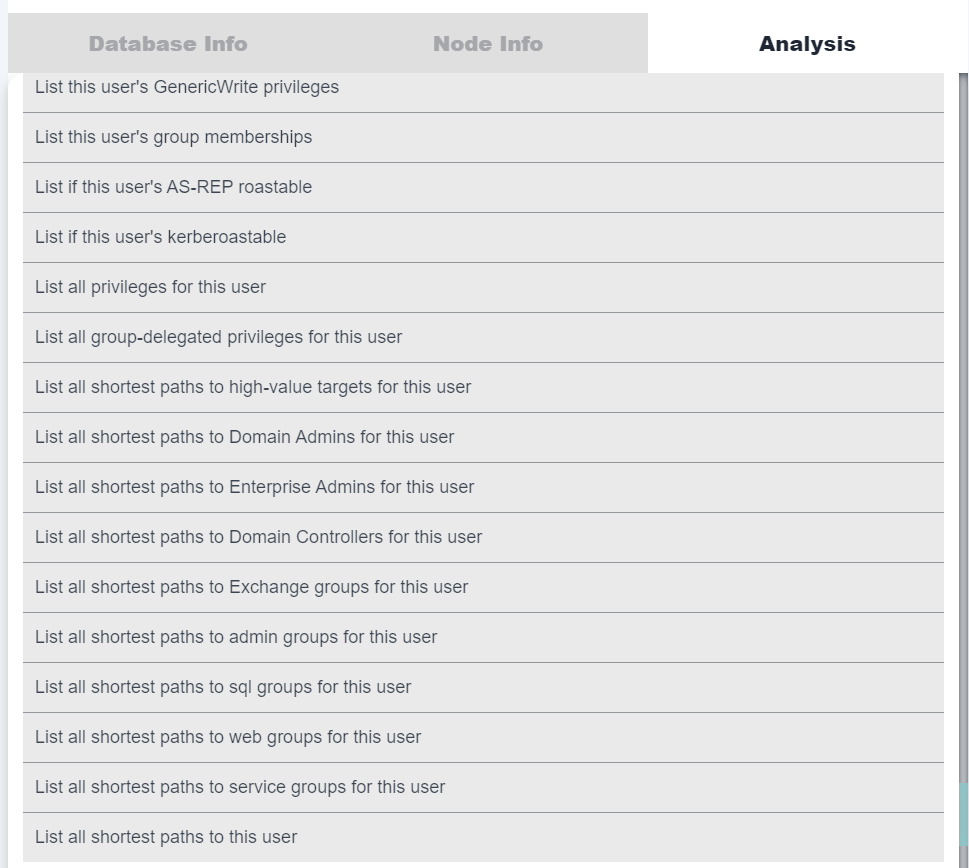
Almost all cyphers included in the terminal application (383 to be exact) have been ported over to json format for direct usage in the GUI. Follow the instructions below in order to begin using them!
Copy the customqueries.json file to ~/.config/bloodhound/
Copy the customqueries.json file to C:\Users\<YourUsername>\AppData\Roaming\bloodhound\
This script will parse a raw export from the terminal application, specifically the cypher to list all user group memberships as an example for how this tool's output can be parsed. You will pass this export as a parameter to the script, a NTDS.dit file, and an output directory. It will then produce .txt files in the output directory for every group name with entries in DOMAIN\USER format, compatible with DPAT. It will then also produce the -g commandline argument to pass to DPAT, allowing the operator to produce group-specific statistics for every group in a domain.
To use the script, you should have two files ready:
- The raw export from the terminal application that retrieves all user group memberships
- A
NTDS.ditfile with lines in the following format:domain\user:RID:LMhash:NTLMhash:::
The script can be run with the following command:
python parse-memberships.py <memberships_filename> <domain> <ntds_filename> <output_directory>where:
parse-memberships.pyis the name of the script file.<memberships_filename>is the file containing the group membership data, exported from terminal application.<domain>is the domain name to be used for parsing the memberships file.<ntds_filename>is thentds.ditfile containing user data.<output_directory>is the directory where the script will output the group files.
This script will read a list of node names from a .txt file and mark them as either owned or high-value in the database.
To use the script, you should have two files ready:
- A line by line
.txtfile containing node names in theBloodHoundformat- For users:
[email protected] - For groups:
[email protected] - For computers:
COMPUTER.DOMAIN.LOCAL
- For users:
- Your configuration file in
jsonformat containing yourNeo4jusername, password, and database (example shown above)
The script has the following options:
-h, --help show this help message and exit
-c CONFIG, --config CONFIG
Config file
-l LIST, --list LIST List of node names
-o, --owned Set target nodes as owned
-v, --high-value Set target nodes as high-value
You need to specify at least -o or -v
- The program is configured to use the default
Neo4jdatabase andURI - Built for
BloodHound 4.3.1, certain edges will not work for previous versions Windowsusers must runpip3 install pyreadline3
On July 15, 2023 I decided to make some changes to the project. After this date, this project will always be kept one version behind the private version for sponsors. Be sure to sponsor me for access to the latest cyphers, features, and bug fixes. By sponsoring me in this tier, you will also get access to additional private repositories I've not released to the public!
- Add cyphers for
Azureedges - Continue to add cyphers when BloodHound releases updates
- Continue to add cyphers
Please be descriptive with any issues you decide to open and if possible provide output (if applicable).