Docker Enterprise 3.0 is the first Containers-as-a-Service platform to offer production-level support for the integrated management and security of both Linux and Windows Server Containers. It is also the first platform to support both Docker Swarm and Kubernetes orchestration.
In this lab we'll use a Docker Enterprise 3.0 cluster. You will have an environment that is either Linux only, or comprised of Windows and Linux nodes. We'll deploy both a Java web application on Linux and a multi-service application that includes both Windows and Linux components using Docker Swarm. Then, we'll take a look at securing and scaling the application. Finally, we will then deploy the app using Kubernetes.
Difficulty: Intermediate (assumes basic familiarity with Docker and Command Line) If you're looking for a basic introduction to Docker, check out https://training.play-with-docker.com
Workshop Time: Approximately 75 minutes
Introduction:
Tasks:
Note: If you are also running the optional Docker Desktop Enterprise exercises, you can complete Tasks 4 and later after you have completed Task 1 above.
- Tasks 2-4 below are optional since you will push an app to DTR and UCP from the desktop.
- Task 5 below should still be completed.
This workshop is only available to people attending a scheduled Docker workshop. This could be arranged through:
- Docker Meetups
- Conference sessions including this workshop
- Special arrangements between your company and Docker.
The workshop organizer will provide you with the URL to a workshop environment that includes Docker Enterprise Edition. The environment will be based on Play with Docker.
If none of these apply to you, contact your local Docker Meetup Chapter and inquire if there are any scheduled workshops. In the interim, you might be interested in the online labs available through the Play with Docker Classroom portal.
There are three main components to the Play With Docker (PWD) interface:
Play with Docker provides access to the 4 Docker Enterprise hosts in your Cluster. These machines are:
- A Linux-based Docker Enterprise 19.XX Manager node
- Three Linux-based Docker Enterprise 19.XX Worker nodes
- A Windows Server 2019-based Docker Enterprise XX.XX Worker Node
In some cases, your workshop organizer will have requested a Linux only environment. In this case, feel free skip the Windows sections of the workshop.
By selecting the nodes in the left panel of the user interface, the console will connect to that node.
Additionally, the PWD screen provides you with a one-click access to the Universal Control Plane (UCP)
web-based management interface as well as the Docker Trusted Registry (DTR) web-based management interface. Clicking on either the UCP or DTR button will bring up the respective server web interface in a new tab.
Throughout the lab you will be asked to provide either hostnames or login credentials that are unique to your environment. The user credentials for both UCPand DTR can be found at the bottom of the PWD screen in the Session Information table.
-
When you encounter a phrase in between
<and>you are meant to substitute in a different value.For instance if you see
<dtr hostname>you would actually type something likeip172-18-0-7-b70lttfic4qg008cvm90.direct.ee-workshop.play-with-docker.com -
Wherever n you see the Linux logo, all the following instructions should be completed in your Linux console
-
Wherever you see the Windows logo, all the subsequent instructions should be completed in your Windows console. These sections can be skipped if you are working with a Linux environment only.
Docker Enterprise provides an integrated, tested and certified platform for apps running on enterprise Linux or Windows operating systems and cloud providers. Docker Enterprise is tightly integrated to the the underlying infrastructure to provide a native, easy to install experience and an optimized Docker environment. Docker Certified Infrastructure, Containers and Plugins are exclusively available for Docker Enterprise with cooperative support from Docker and the Certified Technology Partners.
While it is easy to run an application in isolation on a single machine, orchestration allows you to coordinate multiple machines to manage an application, with features like replication, encryption, load-balancing, service discovery and more. If you've read anything about Docker, you have probably heard of Kubernetes and Docker Swarm mode. Docker Enterprise allows you to use either Docker Swarm mode or Kubernetes for orchestration.
Both Docker Swarm mode and Kubernetes are declarative: you declare your cluster's desired state, and applications you want to run and where, networks, and resources they can use. Docker Enterprise simplifies this by taking common concepts and moving them to the a shared resource.
A Swarm is a group of machines that are running Docker and joined into a cluster. After that has happened, you continue to run the Docker commands you’re used to, but now they are executed on a cluster by a Swarm manager. The machines in a Swarm can be physical or virtual. After joining a Swarm, they are referred to as nodes.
Swarm mode uses managers and workers to run your applications. Managers run the Swarm cluster, making sure nodes can communicate with each other, allocate applications to different nodes, and handle a variety of other tasks in the cluster. Workers are there to provide extra capacity to your applications. In this workshop, you have one manager and three workers.
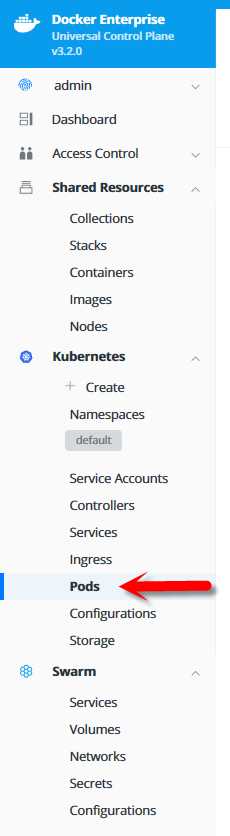
Kubernetes is available in Docker Enterprise 3.0 and included in this workshop. Kubernetes deployments tend to be more complex than Docker Swarm, and there are many component types. UCP simplifies a lot of that, relying on Docker Swarm to handle shared resources. We'll concentrate on Pods and Load Balancers in this workshop, but there's plenty more supported by UCP 3.XX.
The Play with Docker (PWD) environment is almost completely set up, but before we can begin the labs, we need to do two more steps. First we'll add a Windows node to the cluster. We've left the node unjoined so you can see how easy it is to do. Then we'll create two repositories in Docker Trusted Registry. (The Linux worker nodes are already added to the cluster)
-
Navigate to the provided URL using your favorite browser.
-
Fill out the form, and click
submit. You will then be redirected to the PWD environment.It may take a few minutes to provision out your PWD environment. After this step completes, you'll be ready to move on to task 1.2: Install a Windows worker node
Next we are going to add a Windows Server 2016 to the cluster using Docker Swarm.
-
From the main PWD screen click the
UCPbutton on the left side of the screenNote: This Docker Enterprise install uses the default self-signed certs. Because of this, your browser may display a security warning similar to the message below. This message might appear different depending on your web browser. It is safe to 'acknowledge' and proceed.
In a production environment you would use certs from a trusted certificate authority and would not see this screen.
-
When prompted enter your username and password, use the credentials that are located below the console window on the main PWD screen. The UCP web interface will open in your web browser.
Note: Once the main UCP screen loads you'll notice there is a red warning bar displayed at the top of the UCP screen, this is an artifact of running in a lab environment. A UCP server configured for a production environment would not display this warning
-
From the main dashboard screen, click
Add a Nodeon the bottom left of the screen -
Select node type "Windows".
Under the Step 2 section check the box
I have followed the instructions and I'm ready to join my windows node.Next, copy the text from thedocker swarm joincommand from the dark box shown on theAdd Nodescreen. Don't select a custom listen or advertise address.Note There is an icon in the upper right corner of the dark box that you can click to copy the text to your clipboard.
Note: You may notice that there is a UI component to select
LinuxorWindowson theAdd Nodescreen. In a production environment where you are starting from scratch, there are a few prerequisite steps that need to be completed prior to adding Windows node. However, we've already done these steps in the PWD environment. For this lab, just leave the selection onLinuxand move on to step 2 -
Return to the PWD interface and click the name of your Windows node. This will connect the web-based console to your Windows Server 2016 Docker Enterprise host.
-
Paste the text from Step 4 at the command prompt in the Windows console. (depending on your browser, this can be tricky: try the "paste" command from the edit menu instead of right clicking or using keyboard shortcuts)
You should see the message
This node joined a Swarm as a worker.indicating you've successfully joined the node to the cluster.Note If the command failed, verify that the command was correctly entered into the Windows console.
-
Switch back to the UCP server in your web browser and click the
xin the upper right corner to close theAdd Nodewindow -
You will be taken back to the UCP Dashboard. In the left menu bar, click Shared Resources and then select Nodes.
The
Nodesscreen will opeb and you can see 4workernodes and 1managerlisted on your screen.Initially the new worker node will be shown with status
down. After a minute or two, refresh your web browser to ensure that your Windows worker node has come up asHealthy UCP worker
Congratulations on adding a Windows node to your UCP cluster. Your are now ready to use the worker in either a Swarm or Kubernetes. Next, we'll create a few repositories in Docker Trusted registry.
Docker Trusted Registry (DTR) is a special service designed to store and manage your Docker images. In this lab we're going to create three different Docker images, and push them to DTR. Before we can do that, we need to setup repositories in which those images will reside.
However, before we create the repositories, we do want to restrict access to them. Since we have two distinct app components, a Java web app (with a database), and a .NET API, we want to restrict access to them to the team that develops them, as well as the administrators. To do that, we need to create two users and then two organizations.
-
In the PWD web interface, click the
DTRbutton on the left side of the screen.Note: As with UCP before, DTR is also using self-signed certs. It's safe to click through any browser warning you might encounter.
-
From the main DTR page, click users and then the New User button.
-
Create a new user,
java_userand give it a password you'll remember. I useduser1234. Be sure to save the user.Then do the same for a
dotnet_user. You should see a similar users as below. -
In the left Menu, select Organizations
-
Press the
New organizationbutton, name itjava, and click save.Then do the same with dotnet and you'll have two organizations.
-
Now you get to add a repository! Click on the java organization, select Repositories and then
New repository -
Name the repository
java_web. Provide a Description and clickSave.Note the repository is listed as "Public" but that means it is publicly viewable by users of DTR. It is not available to the general public.
-
Now it's time to create a team so you can restrict access to who administers the images. Select the Members Menu Tab and Press
Add userbutton. Start typing in java in the Search by Username box.. Select thejava_userwhen it comes up. SelectSave. -
Next select the
javaorganization and press the Teams Green+button to create awebteam. -
Select the
webTeam and click theAdd userbutton. Add thejava_useruser to thewebteam and click save. -
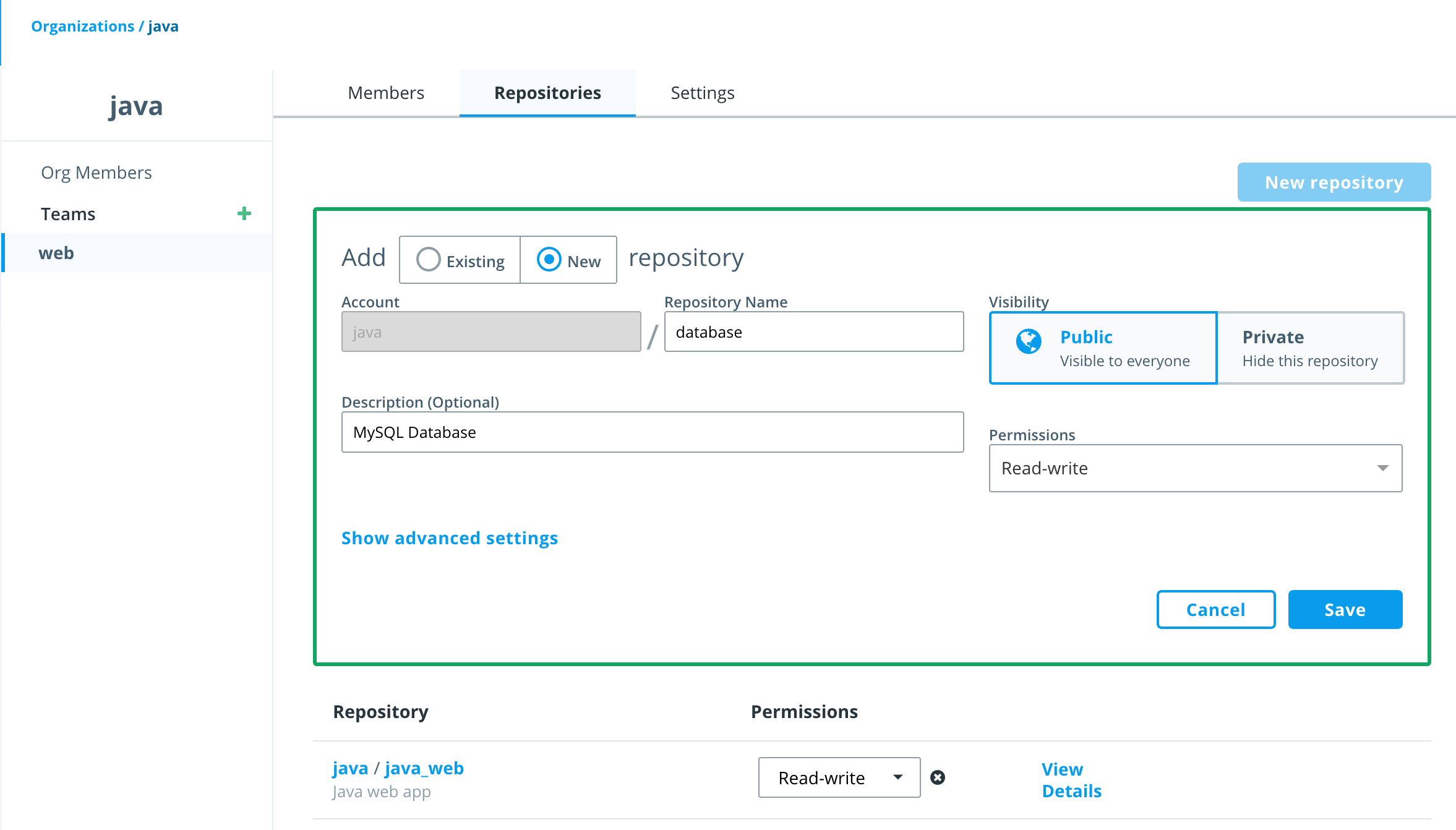
Next select the
webteam and select theRepositoriestab and clickNew repository. SelectAdd Existing repositoryand click in theRepository Namefield and choose thejava_webrepository. You'll see thejavaaccount is already selected. Then selectRead/Writepermissions so thewebteam has permissions to push images to this repository. Finally clickSave. -
Now add a
Newrepository also owned by the web team and call itdatabase. This can be done directly from the web team'sRepositoriestab by clicking theNew repositorybutton, select AddNewrepository and name the repositorydatabase. Be sure to grantRead/Writepermissions for this repository which will be part of thewebteam as well. -
Repeat 4-11 above to create the same structure in the
dotnetorganization. First, create theapiTeam, add thedotnet_useras member to to theapiTeam and create the repositorydotnet_api. Grantread/writepermissions for thedotnet_apirepository to theapiteam. -
From the main DTR page, click Repositories, you will now see all three repositories listed.
-
(optional) If you want to check out security scanning in Task 5, you should turn on scanning now so DTR downloads the database of security vulnerabilities. In the left-hand panel, select
Systemand then theSecuritytab. SelectENABLE SCANNINGmethod for installation and updates isOnlineand clickEnable Online Syncing
Congratulations, you have created three new repositories in two new organizations, each with one team and a user each.
Now that we've completely configured our cluster, let's deploy a web app. The Signup application is a basic Java CRUD (Create, Read, Update, Delete) application that uses Spring and Hibernate to transact queries against MySQL. It runs in Tomcat.
-
From PWD click on the
worker1link on the left to connect your web console to the UCP Linux worker node. Click the terminal window and hit the enter or space key to activate the terminal window. -
Before we do anything, let's configure an environment variable for the DTR URL/DTR hostname. You may remember that the session information from the Play with Docker landing page (Below the terminal window). Select and copy the URL for the DTR hostname.
-
Set an environment variable
DTR_HOSTusing the DTR host name defined on your Play with Docker landing page:export DTR_HOST=<dtr hostname> echo $DTR_HOST
-
Now use git to clone the workshop repository.
git clone https://github.com/dockersamples/hybrid-app.git
You should see something like this as the output:
Cloning into 'hybrid-app'... remote: Counting objects: 389, done. remote: Compressing objects: 100% (17/17), done. remote: Total 389 (delta 4), reused 16 (delta 1), pack-reused 363 Receiving objects: 100% (389/389), 13.74 MiB | 3.16 MiB/s, done. Resolving deltas: 100% (124/124), done. Checking connectivity... done.
You now have the necessary demo code on your worker host.
-
Change into the
java-appdirectory.cd ./hybrid-app/java-app/ -
Use
docker buildto build your Docker image.docker build -t $DTR_HOST/java/java_web .
Note the final "." in the above command. The "." is the build context, specifically the current directory. One of the most common mistakes even experienced users make is leaving off the build context.
The -t tags the image with a tag or name. In our case, the name indicates which DTR server and under which organization's repository the image will reside.
Note: Feel free to examine the Dockerfile in this directory if you'd like to see how the image is being built.
There will be quite a bit of output. The Dockerfile describes a two-stage build. In the first stage, a Maven base image is used to build the Java app. But to run the app you don't need Maven or any of the JDK stuff that comes with it. So the second stage takes the output of the first stage and puts it in a much smaller Tomcat image.
-
Log into your DTR server from the command line.
First use the
dotnet_userand passworduser1234which isn't part of the java organizationdocker login $DTR_HOST Username: <your username> Password: <your password> Login Succeeded
Use
docker pushto upload your image up to Docker Trusted Registry.docker push $DTR_HOST/java/java_webdocker push $DTR_HOST/java/java_web The push refers to a repository [.<dtr hostname>/java/java_web] 8cb6044fd4d7: Preparing 07344436fe27: Preparing ... e1df5dc88d2c: Waiting denied: requested access to the resource is denied
As you can see, the access control that you established in the Task 1.3 prevented you from pushing to this repository.
-
Now try logging in using
java_userand passworduser1234then usedocker pushto upload your image up to Docker Trusted Registry.docker push $DTR_HOST/java/java_webThe output should be similar to the following:
The push refers to a repository [<dtr hostname>/java/java_web] feecabd76a78: Pushed 3c749ee6d1f5: Pushed af5bd3938f60: Pushed 29f11c413898: Pushed eb78099fbf7f: Pushed latest: digest: sha256:9a376fd268d24007dd35bedc709b688f373f4e07af8b44dba5f1f009a7d70067 size: 1363
Success! Because you are using a user name that belongs to the right team in the right organization, you can push your image to DTR.
-
In your web browser head back to DTR and click
View Detailsnext to yourjava_webrepository to see the details of the repository.Note: If you've closed the tab with your DTR server, just click the
DTRbutton from the PWD page. -
Click on
Tagsfrom the horizontal menu. Notice that your newly pushed image is now on your DTR. -
Next, build the MySQL database image. Change into the database directory.
cd ../database -
Use
docker buildto build your Docker image.docker build -t $DTR_HOST/java/database .
Note the final "." in the above command. The "." is the build context, specifically the current directory. One of the most common mistakes even experienced users make is leaving off the build context.
-
Use
docker pushto upload your image up to Docker Trusted Registry.docker push $DTR_HOST/java/database -
In your web browser head back to your DTR server, select your
java/databaserepository and clickTagsfrom the horizontal menu. Notice that your newly pushed image is now in your DTR.
The next step is to run the app in Swarm. Remember, the application has two components, the web front-end and the database. In order to connect to the database, the application needs a password. If you were just running this in development you could easily pass the password around as a text file or an environment variable. But keys and passwords should never be be shared in a production environment. Instead, we're going to create an encrypted secret which will allow us to strictly control access.
-
Go back to the first Play with Docker tab. Click on the UCP button. You'll receive the same
httpswarning that you have before. Acknowledge the warnings and log in. You'll see the Universal Control Panel dashboard. -
There's a lot of information on this page about managing the cluster. You can take a moment to explore around and get familiar with the layout.
Next, click on
Swarmand selectSecrets. -
Click the
Createbutton to access theCreate Secretscreen. Typemysql_passwordinNameandDockercon!!!inContent, then clickCreatein the lower right corner. For production environments, more complex passwords should be used. You'll notice the content box allows you to create structured content that will be encrypted with the secret. -
Next we're going to create two networks. First click on
Networksunder theSwarmsection on the left panel, and selectCreatein the upper right corner of the page. You'll be presented with aCreate Networkform. Name this networkback-tier. Leave everything else the default and clickCreatein the lower right. -
Repeat step 4 but with a new network called
front-tier. -
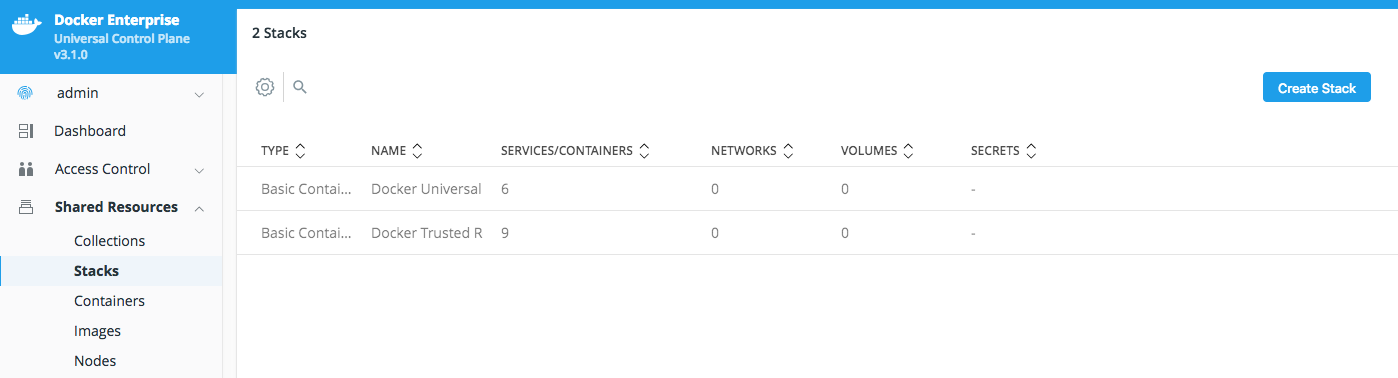
Now we're going to use the fast way to create your application using
Stacks. In the left panel, clickShared Resources->Stacksand thenCreate Stackin the upper right corner. -
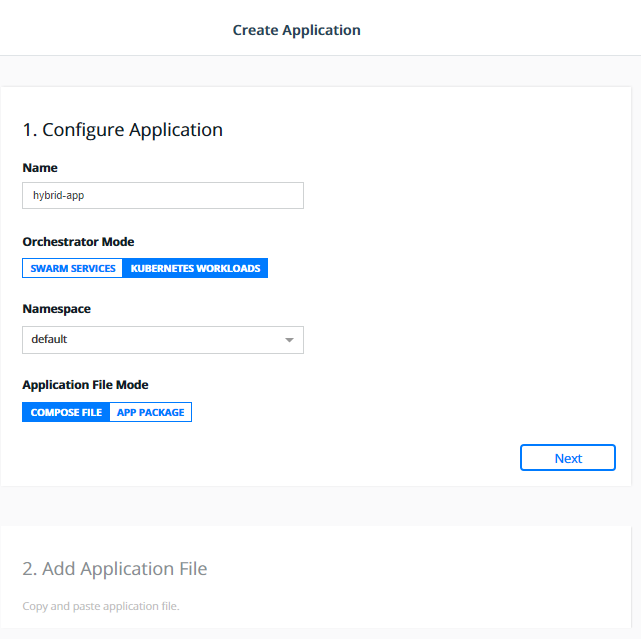
Name your stack
java_weband selectSwarm Servicesfor yourOrchestrator Mode. LeaveApplication File Modeas default, then clickNext.
Below is a sample .yml file that you can use to populate your file.
Note : Before pasting the content into your
compose.ymledit box, you'll need to modify a couple of items. Each of the images is defined as<dtr hostname>/java/<something>, which you'll need to change to the<dtr hostname>found on the Play with the Docker landing page for your session.
It will look something like this:
ip172-18-0-21-baeqqie02b4g00c9skk0.direct.ee-beta2.play-with-docker.com
This can be done right from the
Add Application Fileedit box on theUCP Create Applicationform.
version: "3.3"
services:
database:
image: <dtr hostname>/java/database
# set default mysql root password, change as needed
environment:
MYSQL_ROOT_PASSWORD: mysql_password
# Expose port 3306 to host.
ports:
- "3306:3306"
networks:
- back-tier
webserver:
image: <dtr hostname>/java/java_web
ports:
- "8080:8080"
networks:
- front-tier
- back-tier
networks:
back-tier:
external: true
front-tier:
external: true
secrets:
mysql_password:
external: trueThen click Create in the lower right corner of the window.
Once deployed, click Done.
You might see a websocket error, but the stack is still being created. You can safely ignore this error.
- Congratulations! You've deployed your first app! Now it's time to go and test the functionality. Open a new tab or browser window and enter the
UCP Hostnameand append:8080/java-webto the end of the URL.
E.g. http://ip172-18-0-21-baeqqie02b4g00c9skk0.direct.ee-beta2.play-with-docker.com:8080/java-web
- Delete your
java_webapplication stack.
Now that the app has been moved and updated, we'll be adding an user sign-in API. To illustrate Docker Enterprise's cross-platform capabilities, we'll be performing this deployment using a Windows container.
If your workshop organizer requested a Windows only environment, you can skip ahead to Task 4.
-
Because this is a Windows container, it has to be deployed on a Microsoft Windows host. Switch back to the main Play with Docker page and select the name of the Windows worker.
First verify that Docker is
running- it runs as a background Windows Service. This can be done by the following command:Get-Service dockerIf the service is not running, it can be started with the following command:
Start-Service dockerNext, clone the repository again onto this host:
PS C:\> git clone https://github.com/dockersamples/hybrid-app.git
-
Set an environment variable for the DTR host name. Similar to what you did for the Java app, this will simplify a few steps. Copy the DTR host name again and create the environment variable. For instance, if your DTR host FQDN is
"ip172-18-0-17-bajlvkom5emg00eaner0.direct.ee-beta2.play-with-docker.com"you would type:
PS C:\> $env:DTR_HOST="ip172-18-0-17-bajlvkom5emg00eaner0.direct.ee-beta2.play-with-docker.com"Note ensure the DTR hostname includes quotes otherwise the command will fail
""
-
Change your path to
c:\hybrid-app\netfx-api.PS C:\> cd c:\hybrid-app\netfx-api\
-
Use
docker buildto build your Windows image.PS C:\hybrid-app\netfx-api> docker build -t $env:DTR_HOST/dotnet/dotnet_api .
Note the final "." in the above command. The
"."is the build context, specific to the current directory. One of the most common mistakes even experienced users make is leaving off the build context.Note: Feel free to examine the Dockerfile in this directory if you'd like to see how the image is being built.
Your output should be similar to what is shown below
PS C:\hybrid-app\netfx-api> docker build -t $env:DTR_HOST/dotnet/dotnet_api . Sending build context to Docker daemon 415.7kB Step 1/8 : FROM microsoft/iis:windowsservercore-10.0.14393.1715 ---> 590c0c2590e4 <output snipped> Removing intermediate container ab4dfee81c7e Successfully built d74eead7f408 Successfully tagged <dtr hostname>/dotnet/dotnet_api:latest
Note: It will take a few minutes for your image to build.
-
Log into the Docker Trusted Registry
PS C:\hybrid-app\netfx-api> docker login $env:DTR_HOST Username: dotnet_user Password: user1234 Login Succeeded
-
Push your new image up to Docker Trusted Registry(DTR).
PS C:\hybrid-app\netfx-api> docker push $env:DTR_HOST/dotnet/dotnet_api The push refers to a repository [<dtr hostname>/dotnet/dotnet_api] 5d08bc106d91: Pushed 74b0331584ac: Pushed e95704c2f7ac: Pushed 669bd07a2ae7: Pushed d9e5b60d8a47: Pushed 8981bfcdaa9c: Pushed 25bdce4d7407: Pushed df83d4285da0: Pushed 853ea7cd76fb: Pushed 55cc5c7b4783: Skipped foreign layer f358be10862c: Skipped foreign layer latest: digest: sha256:e28b556b138e3d407d75122611710d5f53f3df2d2ad4a134dcf7782eb381fa3f size: 2825
-
Verify your newly pushed image within the DTR web interface.
-
Firstly, we need to update our Java web app to take advantage of the .NET API. Switch back to
worker1and change directories to thejava-app-v2directory. Repeat steps 1,2, and 4 from Task 2.2 but add a tag:2to your build and pushes:$ docker login username: java_user password: user1234 $ docker build -t $DTR_HOST/java/java_web:2 . $ docker push $DTR_HOST/java/java_web:2
Note the final "." in the above
docker buildcommand. The "." is the build context, specifically the current directory. One of the most common mistakes even experienced users make is leaving off the build context.This will push a different version of the app, version 2, to the same
java_webrepository. -
Next repeat the steps 6-8 from Task 2.3, but use this
Composefile instead:Note : Before pasting the content into your
compose.ymledit box, you'll need to modify a couple of items. Each of the images is defined as<dtr hostname>/java/<something>, which you'll need to change to the<dtr hostname>found on the Play with the Docker landing page for your session.It will look something like this:
ip172-18-0-21-baeqqie02b4g00c9skk0.direct.ee-beta2.play-with-docker.comThis can be done right from the
Add Application Fileedit box on theUCP Create Applicationform.version: "3.3" services: database: image: <dtr hostname>/java/database # set default mysql root password, change as needed environment: MYSQL_ROOT_PASSWORD: mysql_password # Expose port 3306 to host. ports: - "3306:3306" networks: - back-tier webserver: image: <dtr hostname>/java/java_web:2 ports: - "8080:8080" networks: - front-tier - back-tier environment: BASEURI: http://dotnet-api/api/users dotnet-api: image: <dtr hostname>/dotnet/dotnet_api ports: - "57989:80" networks: - front-tier - back-tier networks: back-tier: external: true front-tier: external: true secrets: mysql_password: external: true
Congratulations, you deployed a multi-acrhictecture application on Docker Swarm
-
Navigate to
Shared Resources -> Stacks -> java_webthen click theservicestab. -
After a couple mintues you should see all the services green and deplyoed.
-
Once tested, delete the stack.
Now that we have built, deployed and scaled a multi OS application to Docker Enterprise using Swarm mode for orchestration, let's look at how to use Docker Enterprise with Kubernetes.
Docker Enterprise lets you choose the orchestrator used to deploy and manage your application between Swarm and Kubernetes. In the previous tasks we've used Swarm for our orchestration. In this section we will deploy the application to Kubernetes and see how Docker Enterprise exposes Kubernetes concepts.
Before moving forward we need to make sure that our cluster worker nodes can schedule Kubernetes workloads. Navigate to the nodes section:
-
UCP > Shared Resources > NodesYou'll notice that the scheduler type of
worker2andworker3is set to Swarm.Click on the
worker2node and change it's orchestration type tomixedusing the gear icon on the top right corner and clickSave.Repeat the same step for
worker3.Now your cluster is configured to run both Kuberentes and Swarm workloads
For now Kubernetes does not support Windows workloads in production, so we will start by porting the .NET part of our application to a Linux container using .NET Core.
-
From the Play with Docker landing page, click on
worker1and CD into thehybrid-app/dotnet-apidirectory.cd ~/hybrid-app/dotnet-api/
-
Use
docker buildto build your Linux image.docker build -t $DTR_HOST/dotnet/dotnet_api:core .
Note the final "." in the above command. The "." is the build context, specifically the current directory. One of the most common mistakes even experienced users make is leaving off the build context.
Note: Feel free to examine the Dockerfile in this directory if you'd like to see how the image is being built. Also, we used the
:coretag so that the repository has two versions, the original with a Windows base image, and this one with a Linux .NET Core base image.Your output should be similar to what is shown below
Sending build context to Docker daemon 29.7kB Step 1/10 : FROM microsoft/aspnetcore-build:2.0.3-2.1.2 AS builder 2.0.3-2.1.2: Pulling from microsoft/aspnetcore-build 723254a2c089: Pull complete <output snipped> Removing intermediate container 508751aacb5c Step 7/10 : FROM microsoft/aspnetcore:2.0.3-stretch 2.0.3-stretch: Pulling from microsoft/aspnetcore Successfully built fcbc49ef89bf Successfully tagged ip172-18-0-8-baju0rgm5emg0096odmg.direct.ee-beta2.play-with-docker.com/dotnet/dotnet_api:latest
Note: It will take a few minutes for your image to build.
-
Log into Docker Trusted Registry
$ docker login $DTR_HOST Username: dotnet_user Password: user1234 Login Succeeded -
Push your new image up to Docker Trusted Registry.
$ docker push $DTR_HOST/dotnet/dotnet_api:core The push refers to a repository [<dtr hostname>/dotnet/dotnet_api] 5d08bc106d91: Pushed 74b0331584ac: Pushed e95704c2f7ac: Pushed 669bd07a2ae7: Pushed d9e5b60d8a47: Pushed 8981bfcdaa9c: Pushed 25bdce4d7407: Pushed df83d4285da0: Pushed 853ea7cd76fb: Pushed 55cc5c7b4783: Skipped foreign layer f358be10862c: Skipped foreign layer latest: digest: sha256:e28b556b138e3d407d75122611710d5f53f3df2d2ad4a134dcf7782eb381fa3f size: 2825
-
You may check your repositories in the DTR web interface to see the newly pushed image.
Docker Enterprise lets you deploy Kubernetes applications natively using the Kubernetes deployment descriptors. This can be done by providing the yaml files in the UI, or using the kubectl CLI tool.
However, many developers choose docker-compose to build and test their applications. Having to create Kubernetes deployment descriptors as well as maintaining them in sync with the Docker Compose file, is a tedious and error prone process.
In order to simply developent and operations tasks, Docker Enterprise lets you deploy an application defined with a Docker Compose file as a Kubernetes workload. Internally Docker Enterprise uses the official Kubernetes extension mechanism by defining a Custom Resource Definition (CRD) defining a stack object. When you post a Docker Compose stack definition to Kubernetes in Docker Enterprise, the CRD controller takes the stack definition and translates it to Kubernetes native resources like pods, controllers and services.
We'll use a Docker Compose file to instantiate our application. This is the same file you used in a prior task, with a few changes.
- We will switch the .NET Docker Windows image with the .NET Core Docker Linux image we just built.
- Create a new secret
mysql-secretwithDockerCon!!!as the password.
Follow the instructions above but use - instead of _ as Kubernetes doesn't allow underscores.
Let's look at the Docker Compose file in app/docker-stack.yml.
version: '3.3'
services:
database:
deploy:
placement:
constraints:
- node.platform.os == linux
image: <dtr hostname>/java/database
environment:
MYSQL_ROOT_PASSWORD: mysql-password
networks:
back-tier:
ports:
- published: 32768
target: 32768
dotnet-api:
deploy:
placement:
constraints:
- node.platform.os == linux
image: <dtr hostname>/dotnet/dotnet_api:core
networks:
back-tier:
ports:
- published: 32769
target: 80
java-web:
deploy:
placement:
constraints:
- node.platform.os == linux
image: <dtr hostname>/java/java_web:2
environment:
BASEURI: http://dotnet-api/api/users
networks:
back-tier:
front-tier:
ports:
- published: 32770
target: 8080
networks:
back-tier:
external: true
front-tier:
external: true
secrets:
mysql-password:
external: true- Create a new secret
UCP -> Swarm -> SecretsCreate a secretmysql-secretwithDockerCon!!!as the password
- Login to UCP, and select
Shared resources > Stacks.
- Click
Create Stack. Fill name:hybrid-app, mode:Kubernetes Workloads, namespace:Default.
- Copy the below
app/docker-stack.ymlinto theAdd Application Filewindow and clickCreate
**NOTE: **Change the images for the dotnet-api and java-app services for the ones we just built. And remember to change
<dtr hostname>to the long DTR hostname listed on the landing page for your Play with Docker instance.
version: '3.3'
services:
database:
deploy:
placement:
constraints:
- node.platform.os == linux
image: <dtr hostname>/java/database
environment:
MYSQL_ROOT_PASSWORD: mysql-password
networks:
back-tier:
ports:
- published: 32768
target: 32768
dotnet-api:
deploy:
placement:
constraints:
- node.platform.os == linux
image: <dtr hostname>/dotnet/dotnet_api:core
networks:
back-tier:
ports:
- published: 32769
target: 80
java-web:
deploy:
placement:
constraints:
- node.platform.os == linux
image: <dtr hostname>/java/java_web:2
environment:
BASEURI: http://dotnet-api/api/users
networks:
back-tier:
front-tier:
ports:
- published: 32770
target: 8080
networks:
back-tier:
external: true
front-tier:
external: true
secrets:
mysql-password:
external: true- To see the stack being created, navigate to
Kubernetes > Pods. You should see the stack being created.
- Click on the
hybrid-appstack to see the details.
- Navigate to
Kubernetes > Podto verify the pods are being deployed.
- Navigate to
Kubernetes > Controllersto verify the deployments and ReplicaSets.
- Navigate to
Kubernetes > Load Balancersto verify the Kubernetes services that have been created.
- Click on
java-web-publishedto the the details of the public load balancer created for the Java application.
- The
Node Port32770 is exposed. Note that this is different than previous implementations due to Kubernetes NodePort range limitations. Open a new browser tab, paste in theUCP Hostnamefrom the Play with Docker landing page and add:32770/java-web/at the end of the url. You should be led to the running application.
Security is crucial for all organizations and covers a wide range of topics. Far too many to cover them in-depth in this workshop. We'll be examining just one of the features that Docker Enterprise provides to assist you in building a secure software supply chain: Image Scanning which checks for vulnerabilities in your images.
-
If you turned on security in Task 1.3 step 14 you can skip this step. Otherwise, proceed to enable scanning now to allow DTR to download the latest security and vulnerabilities database. On the left-hand panel, select
Systemand then theSecuritytab. SelectENABLE SCANNINGand clickEnable Online Syncingto start the download of database of security vulnerabilities.
Note: This will take awhile so you may want to take a break by reading up on Docker Security.
-
Once the security database has downloaded, you can scan individual images. Select a repository, such as
java/java_web, and then select theTagstab. If it hasn't already scanned, selectStart scan. If it hasn't scanned already, this can take 5-10 minutes or so.Note all the vulnerabilities found! This is due to deliberately using an old version of the
tomcatbase image.Most operating systems and many libraries contain some vulnerabilities. The details of these vulnerabilities and when they come into play are important. You can select
View detailsto get additional information. Vulnerabilities within your image layers can be identified here.By selecting
Components, you can see what the vulnerabilities are and what components introduced the vulnerabilities. You can also select the vulnerabilities and examine them in the Common Vulnerabilities and Exploits database. -
Another way reduce your vulnerabilities is to identify the vulnerability origin. For example, you can see that in
java_web:latest, 1 Critical and 9 Major issues were introduced with the Spring Framework. Time to upgrade that framework! Of course, upgrading the app is out of scope for this workshop, but you can see how this would give you the needed information to mitigate vulnerabilities. -
You can also choose newer base images. For example, you can revisit to the Dockerfile in the
~/hybrid-app/java-appdirectory, and change the second base image to9.0.13-jre11-slim. Slim images in official images are generally based on lighter-weight operating systems likeAlpine LinuxorDebian, which have reduced attack vector. Then check the scanning again (this may again take 5-10 minutes). You might still see some vulnerabilities, however, there should be fewer. -
To enable scanning of images automatically, select a repository. Navigate to the
Settingstab and selectOn Pushin theImage Scanningsection. This will initiate a scan every time a new image is pushed to this repository. -
DTR also allows you to Sign Images and Create promotion policies which prevent users from using images in production that don't meet your criteria, including blocking images with critical and/or major vulnerabilities.
- Confirm that you are setting the environmental variable DTR_HOST to the DTR hostname. The DTR hostname can be found in the PWD session information at the bottom of the PWD page.
In this lab we've looked how Docker Enterprise can help you manage both Linux and Windows workloads whether they be traditional apps you've modernized or newer cloud-native apps, leveraging Swarm or Kubernetes for orchestration.
You can find more information on Docker Enterprise at http://www.docker.com as well as continue exploring using our hosted trial at https://dockertrial.com