This project aims at enforcing privacy and security of Firefox without forking the project.
Librefox uses more than 500 privacy/security/performance settings, patches, Librefox-Addons (optional) and a cleaned bundle of Firefox (updater, crashreporter and Firefox's integrated addons that don't respect privacy are removed).
- Updated browser: because this project is not a fork, it is kept updated with the latest Firefox version.
- Extensions firewall: limit internet access for extensions (firewall-test-feature)
- IJWY (I Just Want You To Shut Up): embedded server links and other calling home functions are removed (zero unauthorized connection by default).
- User settings updates: gHacks/pyllyukko base is kept up to date.
- Settings protection: important settings are enforced/locked within
mozilla.cfgandpolicies.json, those settings cannot be changed by addons/updates/Firefox or unwanted/accidental manipulation; To change those settings you can easily do it by editingmozilla.cfgandpolicies.json. - Librefox-addons: set of optional Librefox extensions
- Statistics disabled: telemetry and similar functions are disabled
- Tested settings: settings are performance aware
- ESR and Tor version (Librefox TBB Beta)
- Tor Librefox-addons: adapted Librefox extensions for TBB
- Multi-platform (Windows/Linux/Mac/and soon Android)
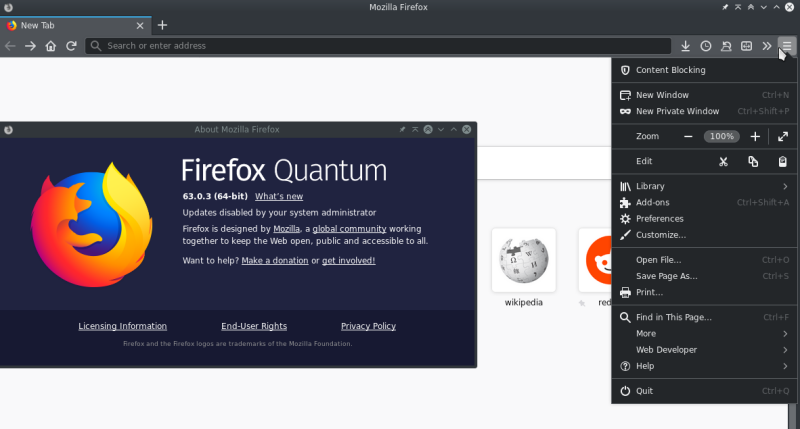
- Dark theme (classic and advanced)
- Recommended and code reviewed addons list
- Community-Driven
- And much more...
> Librefox: Features ............................................................... > Librefox: Download ............................................................... > Librefox: Capture ................................................................ > Addons: Librefox Addons .......................................................... > Addons: Recommended Addons ....................................................... > Addons: Recommended Addons Settings .............................................. > Addons: Reviewing Addons Source Code ............................................. > Addons: Other Useful Addons Listing .............................................. > Wiki: Installation Instructions .................................................. > Wiki: Extensions Network Firewall ................................................ > Wiki: IJWY (I Just Want You To Shut Up) .......................................... > Wiki: Edit Locked Settings ....................................................... > Wiki: Settings Index ............................................................. > Wiki: Cookies Settings ........................................................... > Wiki: Tracking Protection ........................................................ > Wiki: Comparing Changes And Updates .............................................. > Wiki: Documentation .............................................................. > Wiki: Librefox Dark Theme ........................................................ > Wiki: Tuning Librefox ............................................................ > Wiki: Librefox ESR ............................................................... > Wiki: Tor Compatibility .......................................................... > Wiki: DRM Compatibility .......................................................... > Wiki: Building And Packaging ..................................................... > Browser Tests: Security/Fingerprint .............................................. > Browser Tests: Performance ....................................................... > Browser Tests: DNS/VPN/Proxy Leak ................................................ > Infos: Librefox Roadmap .......................................................... > Infos: Changelog ................................................................. > Infos: About .....................................................................
Important notice: this is a temporary version, awaiting a correct build of the project, Librefox is distributed as a configuration files for Firefox. To apply Librefox configuration to Firefox extract the compressed file to Firefox's installation directory (detailed installation instructions). Future Librefox version will be independant from Firefox and therefore will solve this issue.
Linux
-
Librefox-2.1-Firefox-Linux-64.0.0.zip - 40.0 KB - SHA1: a6f36d4c55c096f7e67c7cbf500ebb0fca9a0d2a
-
Librefox-2.1-Tor-Linux-v8.0.4-Beta.zip - 62.3 KB - SHA1: 43fe17592565bb2c5802dd48c9746a3f12d7dd1a
Windows
-
Librefox-2.1-Windows-64.0.0.zip - 40.0 KB - SHA1: a0fba18cc79c95bde483fdb7cd91c1171bc5b7bf
-
Librefox-2.1-Tor-Windows-v8.0.4-Beta.zip - 62.3 KB - SHA1: c72787e009d1a264ae53f4d76d0ffc464cfef7eb
Mac
-
Librefox-2.1-Mac-60.4.0.zip - 40.0 KB - SHA1: 467e56a4fcf4e99a1a66377d9f0221cdcd748748
-
Librefox-2.1-Tor-Mac-v8.0.4.zip - 60.7 KB - SHA1: 4c3d848d6d43e28ad7ddfb3d3e2e26ca590c950b
Librefox addons are not bundled and need to be installed manually
- Librefox Dark Theme: Dark theme
- Librefox HTTP Watcher: Change the url bar color on HTTP sites
- Librefox Reload Button: Add a reload button to URL-bar instead of the toolbar
Recommended addons are not bundled and need to be installed manually
- Cookie Master: Block all cookies and only allow authorized sites
- First Party Isolation: Enable/Disable FPI with the click of a button
- User Agent Platform Spoofer: Spoof a different UserAgent OS Linux/Windows/Mac
- Browser Plugs Privacy Firewall: Sets of settings to prevent fingerprinting and security issues
- uBlock Origin + IDCAC List + Nano-Defender List: Block web advertisement and tracking
uBlock: Additional filters are availables here: https://filterlists.com/ (don't surcharge it to avoid performance loss)
Browser Plugs Privacy Firewall: Keep settings light to make privacy.resistFingerprinting efficient because too much customization will lead to uniqueness and therefore easy fingerprinting.
- Privacy / Fingerprint / Fake values for getClientRects
- Privacy / Fingerprint / Randomize Canvas Fingerprint
- Privacy / Fingerprint / 100% Randomize ALL Fingerprint Hash
- Firewall / Experimental / Block SVG getBBox and getComputedTextLength
- Privacy / Font / Randomize
- Privacy / Font / Enable protection for font and glyph fingerprinting
Recommended extensions code have been reviewed for potential unwanted behaviour... reviewed version are available under extensions directory.
Extensions Firewall - Description
This is a test experiment feature and it is disabled by default !!! A new section Extensions Manager is added to manage addons globally (and addons networking in the subsection Extensions Firewalling). Firewalling the network for addons is doable, but it requires a considerable amount of additional work in Librefox to make it usable through a button or in a per addon basis (this may or may not be added in a future version, it also could be abandoned as it is a test feature). Currently you can block a list of domains or block the whole network for all the extensions.
Extensions Firewall - The Settings
Available native network restriction settings for addons:
- Restricted domains list:
extensions.webextensions.restrictedDomainsthis is a list of restricted domains that will be used to block some hosts for all the extensions, Firefox uses this setting to block extensions from accessing mozilla's domains/sites, by default in Librefox this setting is set to allow extensions to access all the web (You can edit that list to match your needs or to block a specific domain, note that the domain name has to be 'exact' (for instance facebook.com will only block facebook.com not mobile.fabcebook.com) - Content security policy:
extensions.webextensions.base-content-security-policyandextensions.webextensions.default-content-security-policythe later settings can be redefined/changed within an extension so it's not efficient for a firewall purpose. CSP settings are used in Firefox as an added layer of security that helps to detect and mitigate certain types of attacks, including Cross Site Scripting (XSS) and data injection attacks. These attacks are used for everything from data theft to site defacement to distribution of malware; In short: CSP settings block and allow certain domains under certain circumstances and thus could be used to firewall the extensions (CSP Documentations, its sources code and implementation)
Extensions Firewall - Blocking A Domain
Edit the restricted domains setting as follow under the about:config page:
- Restricted Domains Setting:
extensions.webextensions.restrictedDomainsValue:ExactDomains1,ExactDomains2,ExactDomains3etc.
Extensions Firewall - Blocking The Network
To enable the feature and block the network for all the extensions open mozilla.cfg search for Enable-Firewall-Feature-In-The-Next-Line and remove the // in the next line.
Note that this will block the network access for all the extensions and a lot of extensions needs to be connected in order to work. In the current version of Librefox you can block the network for all the extensions or allow it for all of them, a future version may provide additional features like "per addon" setting (By default Librefox allows networking for extensions).
Extensions Firewall - More Infos
Check debug-check-todo.log for additional info about future version and researches about the subject. Also check CSP Documentations, its sources code and implementation.
This is a set of settings that aim to remove all the server links embedded in Firefox and other calling home functions in the purpose of blocking un-needed connections. The objective is zero unauthorized connection (ping/telemetry/Mozilla/Google...).
Available in the releases page
Notice: in the current state of the project Librefox is a set of configuration files for Firefox (awaiting a correct build of the project), therefore if you already have a Firefox profile, that profile will be used and temporary files will be removed (cookies and current session), make sure to backup your current Firefox's profile before using Librefox. Using Librefox simultaneously with Firefox is possilbe through a different profile you can follow this wiki to do so. Future Librefox version will be independant from Firefox and therefore will solve this issue.
Windows
- Download and install the last version of Firefox x32 release or x64 release
- Download Librefox zip file and extract it
- Locate Firefox's installation directory (where the firefox.exe is located)
C:\Program Files\Mozilla Firefox\orC:\Program Files (x86)\Mozilla Firefox\orTor-Install-Directory\Browser\ - Copy the extracted Librefox files to the install directory
Linux
- Download and extract the last version of Firefox x32 release or x64 release
- Download Librefox zip file and extract it
- Copy the extracted Librefox files to the newly downloaded
firefoxdirectory - You can use directly Librefox by running 'firefox/firefox'
- You can as well create a shortcut to 'firefox/firefox' to open Librefox easily.
Mac
- Download and install the last version of Firefox
- Download Librefox zip file and extract it
- Locate Firefox's installation directory (
Applications/Firefox.app/Contents/Resources/orApplications/Tor Browser.app/Contents/Resources/) - Copy the extracted files to the install directory
Just edit mozilla.cfg, save and restart Librefox.
Firefox 60 and privacy.resistFingerprinting are relatively new, please give it some time to be more widely used and thus less finger-printable; If you are using a different site to analyze your browser make sure to read and understand what the test is about.
- SSLLabs
- AmiUnique
- BrowserLeaks
- BrowserPlugs
- FingerPrintJS2
- Third-Party-Cookies
- Testing-Notifications
- Browser-Storage-Abuser
- Service-Workers-Push-Test
Performance tests can be done here LVP Octane, it needs to be launched alone with other applications closed and with no other activity but the benchmark, also it's recommended to launch it many times and then calculate the average.
License: Mozilla Public License 2.0
Inspired from: ungoogled-chromium
Author: Intika (from Liege/Belgium), contact: [email protected]
Donation: Paypal - [email protected] if you like it you can offer me a coffee :)
Based on: gHacks-user.js, pyllyukko-user.js and privaconf big thanks to everyone.
Acknowledgment, special thanks to:
- The Mozilla team for their amazing work on Firefox
- The gHacks-User team for allowing the usage of their work
- Martin Brinkmann (gHacks.net) for writing on Librefox
- All users that are encouraging this project by starring it
- And everyone who is helping this project: @brainscar, @Eloston, @dimqua, @Atavic, @antuketot76, @nhynes, @maxidor, @samuel8941, @shaynem, @szepeviktor, and all the others i forget to mention.
Objectives for future versions of Librefox (this may change)
- Develop an all-in-one Librefox addon to rule them all ? (Normal & Tor Version… this would simplify Librefox)
- Develop an easy to use firewall system for extensions (button/hosts/allow/deny/per-addon)
- Develop an advanced settings page
- Fix mozilla legal issue
- Update checker extension (feature in the full extension ?)
- Advertisement for the project to reach more users ?
Todo for future versions of Librefox (this may change)
- Listed under issues section
// ==============================
// Index mozilla.cfg .......... :
// ==============================
//
// ---------------------------------------------------------------------
// Section: User settings // Bench Diff: +0 / 5000
// Section: Defaulting Settings // Bench Diff: +0 / 5000
// ------------------------------------------
// Section: Controversial // Bench Diff: +0 / 5000
// Section: Firefox Fingerprint // Bench Diff: +0 / 5000
// Section: Locale/Time // Bench Diff: +0 / 5000
// Section: Ghacks-user Selection // Bench Diff: +100 / 5000
// Section: Extensions Manager // Bench Diff: +0 / 5000
// Section: IJWY To Shut Up // Bench Diff: +0 / 5000
// Section: Microsoft Windows // Bench Diff: +0 / 5000
// Section: Firefox ESR60.x // Bench Diff: +0 / 5000
// ------------------------------------------
// Section: Security 1/3 // Bench Diff: +0 / 5000
// Section: Security 2/3 // Bench Diff: +0 / 5000
// Section: Security 3/3 (Cipher) // Bench Diff: +0 / 5000
// ------------------------------------------
// Section: Performance 1/5 // Bench Diff: +650 / 5000
// Section: Performance 2/5 // Bench Diff: -800 / 5000
// Section: Performance 3/5 // Bench Diff: -1720 / 5000
// Section: Performance 4/5 // Bench Diff: -200 / 5000
// Section: Performance 5/5 // Bench Diff: -50 / 5000
// ------------------------------------------
// Section: General Settings 1/3 // Bench Diff: +100 / 5000
// Section: General Settings 2/3 // Bench Diff: +0 / 5000
// Section: General Settings 3/3 // Bench Diff: -40 / 5000
// ------------------------------------------
// Section: Disabled - ON/OFF // Bench Diff: +0 / 5000
// Section: Disabled - Deprecated Active // Bench Diff: +0 / 5000
// Section: Disabled - Deprecated Inactive // Bench Diff: +0 / 5000
// ---------------------------------------------------------------------
// ==============================
// Index local-settings.js .... :
// ==============================
//
// ---------------------------------------------------------------------
// Section: General Settings // Bench Diff: ++ / 5000
// ---------------------------------------------------------------------
Using different web services without cookies is impossible and cookie settings in a browser are very important when it come to privacy, in Librefox the settings are locked to avoid unwanted changes in such an important setting, but they can be easily changed in mozilla.cfg under User Settings: Cookies settings.
Firefox now integrates a tracking protection feature (based on disconnect.me) it's a small content blocking list, the listing can not be edited, this feature is disabled in Librefox. It's recommended to use uBlock Origin instead. This feature is disabled:
- Until it evolves and integrates at least list editing.
- Because double filtering (this + ublock) is not suitable for performance.
You can however easily enable this feature in mozilla.cfg under User Settings: Track Protection (just comment active lines with // or remove the entire section).
If you want to compare changes over updates or if you already have a user.js/mozilla.cfg/policies.json. consider using Compare-UserJS, it's an amazing tool to compare user.js files and output the diffs in detailed breakdown, developed by gHack's very own resident cat, claustromaniac 🐱
Usage: If not on windows install PowerShell then (for example) pwsh Compare-UserJS.ps1 mozilla.cfg user.js (Warning that PowerShell connects to Microsoft sometimes).
Mozilla.cfg: Locking and defaulting Librefox settings for security, privacy and performance.
Policies.json: Policies for enterprise environments (the settings availables with policies.json are limited right now because this is a new feature of Firefox).
Bench diff: Impact on the performance of Librefox, it can be a gain or a loss of performance +100/5000 stand for 2% gained performance and -1500/5000 stand for -30% performance loss.
lockPref: Locked preference can not be changed by extensions or updates, they can only be changed in mozilla.cfg.
Section: Description of the settings section separated by ">>>".
Defaulting VS Enforcing: Defaulted settings can be changed by the user or an extension if permitted within the browser while enforced settings are locked and can not be changed within the browser, enforced settings can be changed in mozilla.cfg.
About:config: http://kb.mozillazine.org/About:config_entries.
Librefox provides a classic dark theme extension (Librefox Dark Theme) but also a purified version of ShadowFox available under dark-theme directory to install it just copy the directory chrome to your Librefox profile directory and then restart Librefox, this will expand the dark theme to internal pages like settings pages.
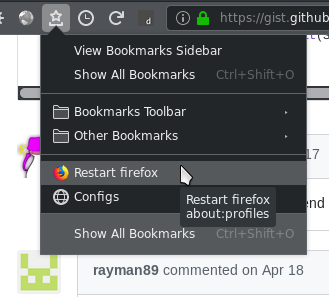
Restart Button
One simple solution is to bookmark about:restartrequired or about:profiles ... when restart is needed open that page and click "normal restart". You can even go further and add the bookmarks links to your icons bar and rename the link to an empty text (you will then have a direct icon to about:profiles and a 2 clicks restart).
Alternative Dark Theme
Linux Fix Text Colors
On Linux when using a dark desktop theme Librefox could display white text over white background or black text on black input on some sites or addons, this is fixed in Librefox with lockPref("ui.use_standins_for_native_colors", true);.
If ui.use_standins_for_native_colors is not enough to fix everything you can fix this issue with an other additional solution by using the following values in about:config (you need to have Adwaita theme installed) more details (Note that this is not needed with the default Librefox settings as it is already fixed)
widget.content.allow-gtk-dark-theme;false
widget.chrome.allow-gtk-dark-theme;false
widget.content.gtk-theme-override;Adwaita:light
Other privacy addons
- NoHTTP: Block http traffic and/or redirect it to https (Excellent remplacment for the unrecommended https-everywhere)
- Google-Container: Open all Google sites in a container
- Facebook-Container: Open all Facebook sites in a container
- Request-Blocker: Hosts style blocking sites
- Decentraleyes: Makes a lot of web resources available locally to improve privacy
- Dont-Track-Me-Google: Cleaning Google search result links
- Canvas-Blocker: Prevent some fingerprinting techniques (This should not be used with browser plugins addon as it provide similar features)
- Cookie-Quick-Manager: View and edit cookies
- Mozilla-Multi-Account-Containers: Manage containers and assign sites to specific container
- Switch-Containers: Switching container for the current tab easily
- Temporary-Containers: Maximizing and automating container potential
- Smart-Referer: Manage referer with a button (Send referers only when staying on the same domain.)
Other useful addons
- Dormancy: Unload tab after a certain time, useful for performance when opening a lot of tabs
- Add Custom Search Engine: Customize your search engine
- ProxySwitcheroo: Apply proxy settings in a click
- UndoCloseTabButton: Reopen last closed tab
- Advanced Github Notifier: Github notifications
- Shortkeys: Add custom shortkeys
- Tabboo: Session manager
Librefox Addons For ESR And Tor
- Librefox HTTP Watcher ESR - Tor MoD: Change the url bar color on http and onion sites (to green/red)
- Librefox NoHTTP - Tor MoD: Block http traffic and/or redirect it to https (Excellent replacement for the unrecommended https-everywhere)
We do not recommend connecting over Tor on Librefox classic version (because of the missing Librefox-Tor-Addons, they are only included in the tor version for obvious reasons), use instead Librefox-Tor version if your threat model calls for it, or for accessing hidden services (Thus said tor settings have been enabled since v2 on all Librefox versions for user toriffying/proxifying their entire connection).
Currently Librefox-TBB is in beta test, Tor compatibility may change.
Digital rights management (DRM) is enforced off by default (this is needed for Netflix and similar); you can enable it with the following instructions:
- Open
mozilla.cfg - Under the section
Section: User Settings - Comment the active lines with
//under the subsectionUser Settings: DRM/CDM - Main - Comment the active lines with
//under the subsectionUser Settings: DRM/CDM - Widevine - Restart Firefox then open
about:preferencesand enablePlay DRM...under general section - Firefox will download Widevine and enable it (under
about:addonsplugins section) you can force the download by clickingCheck for updatesunder the tools button
For ESR users if you opt for Librefox HTTP Watcher you need to use this version Librefox HTTP Watcher ESR - Tor MoD
Linux
Build instruction will be updated soon
Windows
Build instruction will be updated soon
Mac
Build instruction will be updated soon